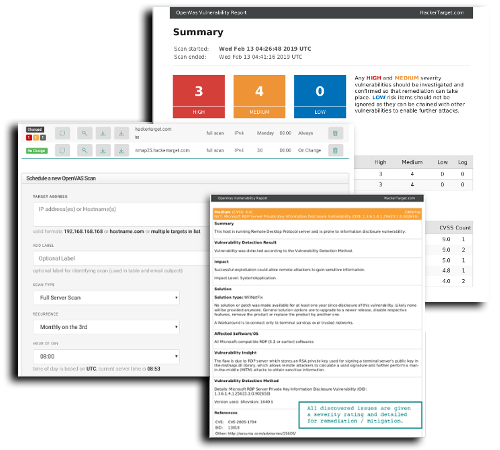
Cyber Chimp, either by request or periodically, can identify, prioritize and report on your IP’s vulnerability posture. We use a variety of systems and tools for your vulnerability assessment (VA) which are updated and maintained daily. These systems have intelligence to inspect an object and identify the known vulnerability. The detailed analysis report provides guidance on remediation options.
Our process:
Once an order has been confirmed, Cyber Chimp engages with you to scope your assessment. This includes the desired IP(s) and rules of engagement including the clients permission to evaluate the risks, timing, and reporting preference. Once confirmed, we start the process and start assessing the risk profile on the assets. Our vulnerability assessment is perform by qualified engineers with a passion in discovering problems. Our systems are updated daily, so as not to miss any potential threats or zerodays. The process will take 24 hours to complete (with the exception of in-depth scans). Finally a report is prepared and submitted for review.
The data is stored for 45 days, with the exception of CyberChimp’s free VA offering. Scan results are dependent on unrestrictive access and public availability. All scans are subject to a point in time scanning.